
How Hackers Walk Right Through Your MFA
It’s Monday morning. You’re at your desk with a coffee. You get an email from Microsoft — your password needs to be updated. You click

It’s Monday morning. You’re at your desk with a coffee. You get an email from Microsoft — your password needs to be updated. You click

You turned on multi-factor authentication. You did the right thing. But here’s the part nobody tells you: hackers have learned to walk right past it.

The Legacy Debt Audit: Identifying the 3 Oldest Risks in Your Server Room Your server room has a secret. It’s not the blinking lights or

Your CRM just doubled its price. You need to leave — but you just realized you can’t take your client data with you. That’s not

That Chrome extension your bookkeeper installed last week? It can read every tab she opens — including your bank portal, your client files, and every

Your bookkeeper just got a LinkedIn message from a “recruiter” at a company she’s never heard of. The job sounds perfect — remote, great pay,

Your home office might be the weakest link in your entire business. If you’re running a small business in Bradenton or Tampa Bay, the laptop

Personal data protection is more important than ever in this digital world. The dark web is a secret part of the internet that is very

Your employees might be the biggest cybersecurity risk in your business – and not just because they’re prone to click phishing e-mails or reuse passwords. It’s because

Your Phone Is Full. Your Files Are One Disaster Away From Gone. You know that annoying message — “Storage Almost Full” — that pops up

If I asked you to name the biggest cybersecurity threats in your office, you’d probably say phishing e-mails, malware or weak passwords. But what if

Planning a vacation this year? Make sure your confirmation e-mail is legit BEFORE you click anything! That’s right, summer is right around the corner and

A client recently asked me, “What mistakes do you see business owners making the most when it comes to IT and cybersecurity?” Oh, where to begin…

Chatbots like ChatGPT, Gemini, Microsoft Copilot and the recently released DeepSeek have revolutionized how we interact with technology, offering assistance with almost every task imaginable
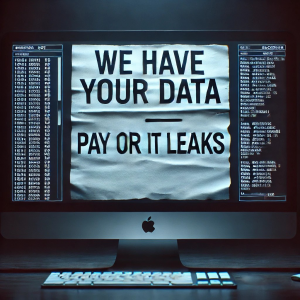
Think ransomware is your worst nightmare? Think again. Hackers have found a new way to hold your business hostage – and it may be even